

Between 1935 and 1949, many North American children (and adults) got their introduction to cryptography through encrypted messages broadcast at the ends of episodes of two popular radio adventure serial programs: Little Orphan Annie and Captain Midnight. Dedicated listeners could join Radio Orphan Annie's Secret Society or (later) Captain Midnight's Secret Squadron, whereupon they would be sent a decoder that would allow them to decrypt each week's messages (generally a clue about what would happen in the next episode).
Orphan Annie (and her Secret Society members) fought crime, battled pirates, solved mysteries, and had other typical American pre-adolescent adventures. Captain Midnight (with his Secret Squadron) used his aviation prowess to perform daring rescues and emergency transports, and, with the outbreak of WWII, was commissioned by the government to lead secret missions behind enemy lines.
The main qualification for membership in (and issuance of a decoder for) Radio Orphan Annie's Secret Society and Captain Midnight's Secret Squadron involved drinking Ovaltine, a malted milk flavoring containing the vitamins and nutrients then understood to be needed by growing secret operatives, or at least to be profitable for its manufacturer (which sponsored the broadcasts). Proof of sufficient Ovaltine consumption was established by mailing in labels from Ovaltine packages. New pins and badges were issued annually, requiring additional labels to be sent in each year. (The devices are sometimes remembered as decoder rings, but in fact they took the form of pins, badges, and the occasional whistle or signal mirror.)
Orphan Annie's Secret Society produced decoders (variously called "Super Decoder pins", "Telematic Decoder Pins" and other names from year to year) from 1935 through 1940. From 1941 through 1949, the decoders were rebranded as "Code-O-Graphs" and distributed by Captain Midnight's Secret Squadron. These years corresponded to Ovaltine's sponsorship of the respective programs. Although the decorative elements and mechanical designs varied, the underlying cryptographic principles were the same for all the decoders.
Encrypted messages were included in the broadcasts roughly once per week, usually at the end of Thursday's show (which typically ended with a cliffhanger). Unfortunately, there does not appear to be an easily available full online archive of the broadcasts. However, you can listen to (and, with the information below, decode) airchecks of several original messages here (note the year to ensure you use the correct decoder badge parameters):
These decoders have endured as iconic examples of simple, "toy" cryptography, even among those (like me) born well after the golden age of radio. And while they are indeed vulnerable to weaknesses that make them unsuitable for most "serious" use, that doesn't mean we shouldn't take them seriously. In fact, the underlying cryptographic and security principles they embody are important and subtle, part of the foundations for much of "modern" cryptography, and the badges combine multiple techniques in interesting ways that repay a bit of careful study. Indeed, they were almost certainly the most cryptologically sophisticated breakfast premiums ever produced. And, by understanding them sufficiently well, we can cryptanalyze and decode messages without needing to buy Ovaltine or scour Ebay. The rest of this post explains how.
Two Basic Cryptographic Techniques
The Orphan Annie and Captain Midnight decoders were based on a combination of two basic cryptographic techniques - the Caesar cipher and the fully permuted monoalphabetic substitution cipher. Those already familiar with classical cryptography will likely want to skim this section and go straight to the good stuff below. But to understand how the decoders work (and how to simulate them), you need to understand these two methods. Fortunately they aren't very difficult or mathematical.
1. The Caesar Cipher
First, let's imagine a very simple encoding of the alphabet, in which we replace each of the 26 letters with a number representing its position:
Ciphertext 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 Plaintext A B C D E F G H I J K L M N O P Q R S T U V W X Y Z
This scheme isn't very secure. In fact, in cryptographic terms, it's not really even encryption, because there's no secret variable that prevents unauthorized people from decoding the messages. It's just an encoding. But we can use it as a starting point for more secure schemes.
In particular, we might "shift" (or "rotate") the alphabet a secret number of positions away from the original numbers (sticking the ones that shifted past the beginning onto the end) So if we shift by one position, the encoding becomes:
Ciphertext 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 Plaintext B C D E F G H I J K L M N O P Q R S T U V W X Y Z A
... while if we shift by 10 positions it becomes:
Ciphertext 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 Plaintext K L M N O P Q R S T U V W X Y Z A B C D E F G H I J
We can now analyze this in cryptographic terms. The letters - the symbols we're encrypting - are called plaintext (or cleartext), while the numbers - the result of encrypting - are called ciphertext. (We don't have to use numbers for ciphertext. We could use any symbols we want, including the original alphabet. But for simplicity, we'll use letters for plaintext and numbers for ciphertext, which is also what the decoder badges did.)
To decrypt a message that was encrypted this way, you have to know (or figure out) by how many positions the alphabet was shifted.
It is hopefully obvious that there are a total of 26 distinct ways to encode the alphabet by this method. We can keep the particular value we used to shift the alphabet when we encrypt a message secret. Cryptographers call this kind of secret encryption parameter the key.
Modern cryptographers usually discuss keys by the bit length of a binary number needed to count all the distinct different keys. In this case, since there are 26 different keys, we'd need a 5 bit number to count them. More precisely, log2(26) = ~4.7. So this scheme can be said to have a 4.7 bit key.
Despite having a key parameter, this technique still isn't very secure by modern standards, because the number of possible key parameters is very small (26). An adversary could just try each one until the decrypted message makes sense, a technique called exhaustive search (for which we named this blog).
But despite this weakness (as well as others), this technique still is very important. It is was invented by (or on behalf of) Julius Caesar, who used it to protect his secret papers. It is arguably the oldest known systematically parameterized (keyed) cryptographic method. And we can combine it with other techniques to build more secure schemes.
2. The Randomly Permuted Monoalphabetic Substitution Cipher
Let's now consider a different method. As before, we'll assign each plaintext letter a corresponding ciphertext number. But this time, we'll randomly scramble - permute - the alphabet rather than keeping it in its original order (as we did with the Caesar cipher). For example:
Ciphertext 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 Plaintext A M Z N B L Y O K C Q X J D R W I E S V H G T F U P
Here, the key is the particular permutation of the alphabet we selected ("AMZNB..."). But even though the encoding and decoding method is similar to what we use with the Ceasar cipher, there are a lot more different possible keys to choose from. The number of distinct permutations of a 26 character alphabet is a number called 26 factorial (written as 26!), calculated as 26*25*24*23*22*21*20*19*18*17*16*15*14*13*12*11*10*9*8*7*6*5*4*3*2, which is a little more than 400,000,000,000,000,000,000,000,000. That's a very large number. It corresponds to a roughly 88 bit key (log2(26!) = ~88.38 bits, to be more precise).
An 88 bit key is large enough to be considered reasonably secure against exhaustive search (trying every possible key) even by modern cryptographic standards, which assume the use of fast, parallel computers. Exhaustive search of such a large keyspace would only be potentially feasible for large governments or extremely well-funded organizations that are willing to devote considerable resources, time, and expense to decrypting your messages.
Unfortunately, the key length is not the whole story for how secure a cipher is (an important cryptographic lesson to remember). Exhaustive search isn't the only way to attack a monoalphabetic substitution scheme. There are several significant shortcuts. The simplest is that they fall completely apart in the presence of known plaintext. That is, if you learn (or can guess) the plaintext corresponding to part of encrypted message (say, that it starts with "THIS MESSAGE IS FOR YOUR EYES ONLY"), you directly learn the plaintext encoding that corresponds to each number used in that part of the ciphertext. In the example permutation above, a ciphertext of 18 always corresponds to a plaintext of E. Once you know the ciphertext that corresponds to a plaintext number, you can decrypt every subsequent occurrence of that number. And you can also rule out that letter for the remaining 25 ciphertext numbers.
Even without known plaintext, this scheme is still weak, because the statistical prevalence of ciphertext numbers will mirror that of the plaintext letters. In normal English text, not all the letters occur equally often (ask a Scrabble player). E is the most common letter, while X is much less common. If you see a lot of 18s in the ciphertext, you can make a good guess that it's more likely an E (or other common letter) than an X. Coupled with other statistical properties of human language, it is often possible to quickly break even relatively short (a few dozen character) messages entirely by hand just by this observation. The message just needs to be long enough for a few of the common letters to become apparent.
So the monoalphabetic substitution cipher isn't, by itself, considered secure by modern standards. But in combination with other methods, it can still, under some circumstances, provide some degree of effective security.
Decrypting Secret Messages
The Orphan Annie and Captain Midnight decoders used a combination of a Caesar cipher and a fully permuted monoalphabetic substitution.
Each year's decoder contained a fixed permutation of the 26 letters of the alphabet, arranged in a ring. With one exception, different years used different permutations. For example, the 1935 Orphan Annie pin used AMZNBLYOKCQXJDRWIESVHGTFUP, while the 1936 pin used AGTPBHMCSQDFZLNEVJYIWUROKX. (I'm showing all the permutations here as starting with the letter "A", but that's an arbitrary choice on my part. Since the alphabet is circular, there's no fixed starting point.)
A second ring contained the numbers from 1 through 26 (in order) that could be independently rotated to any position against the permuted alphabet. This allowed for 26 different mappings between the numbers and the letters. Once set to the correct position, decrypting a message was simply a matter of converting each ciphertext number to the corresponding plaintext letter.
Put in the cryptographic terms we discussed above, the permuted alphabet defined the key for a monoalphabetic substitution cipher (with the 88 bit key changed annually when new decoders were produced with new permutations), while the numeric rotation mechanism allowed it to be further used as a Caesar cipher with the shift value chosen independently for each message.
The physical mechanisms and nomenclature that accomplished this varied from year to year, but the basic method stayed the same: monoalphabetic substitution plus Caesar cipher. The "secret" in each decoder was the particular permutation it used.
To decrypt a message, therefore, it was necessary to know two things: the permutation used that year, and which of the 26 possible rotational positions were used for the message. The permutations were distributed to members as part of the decoders. The Caesar rotation was given at the start of each message.
How the Caesar value was specified varied from year to year depending on certain badge features. In most years, it was given by identifying a single plaintext/ciphertext pair at the correct rotation. To decrypt a message, the recipient would rotate the number wheel until the plaintext letter and ciphertext number lined up and leave it in that position for the rest of the message. Observe that for each of the 26 possible rotations, there are 26 equivalent ways to specify the position. Which letter is used is entirely arbitrary. For example, for the 1935 decoder, A=1 sets the same rotation as P=26.
Several of the badges supported a different way to specify the shift, with an independent indicator that could be set for the correct rotation. These are discussed in the individual badge sections below.
How secure was this scheme? To be sure, neither monoalphabetic substitution nor the Caesar cipher are very secure. They are vulnerable to a range of attacks, and, given sufficient English-language ciphertext, yield to statistical analysis of the distribution of ciphertext symbols. But the individual messages sent in the broadcasts were fairly short - typically 20 to 30 characters long. The use of a different Caesar rotation for different messages could frustrate straightforward frequency analysis from week to week. However, even this combination method is weak by modern standards. I'll leave a detailed security analysis as an exercise to the reader (it's an interesting problem to work out!).
An easier way to decode messages, of course, is with knowledge of the key, either by possessing an official decoder or by learning the secret permutation through espionage or open source intelligence sources (such as the web page you're reading).
Over the years, I've accumulated a complete collection of the 13 different Orphan Annie and Captain Midnight decoders. In the sections that follow, I give each year's secret permutations and other parameters, providing enough information for you to simulate a physical decoder for any year. You can test your decryption skills against the audio clips I linked to at the beginning.
I trust you to use this knowledge for good rather than evil. Happy landings, squadron members!
1935 Radio Orphan Annie Pin


This was the first decoder pin, and the smallest of all the decoders (1.25 inches in diameter). The crossed-keys logo would be right at home on a military cryptanalyst's unit patch.
The permutation is:
The shift value was given by specifying any single number/plaintext pair. (For example, "Set your decoders to R-24".) This permitted any of the 26 possible Caesar rotations to be used.
Note: In the this and the sections that follow, all the decoders are reproduced at the same scale, so you can get an idea of their relative sizes.
1936 Radio Orphan Annie Pin


I like the period art deco design of this pin, and appreciate the hidden feature: a removable secret compartment on the back that can be used to store microfilm, one time pads, poison tablets, or other essential juvenile spycraft paraphernalia. Although larger than the 1935 pin, it was in some ways more discreet, marked only with the initials R.O.A.S.S. Fellow Secret Society members would presumably still easily recognize it.
The permutation is
As before, the Caesar shift was specified via a single number/plaintext pair.
1937 Radio Orphan Annie Pin


The 1937 pin has an ornate decorative startburst design that I like to think was intended to help camouflage its true purpose from untrained eyes. (A secret society is, after all, supposed to be secret.) The rotating disk has small holes above each number that reveal the corresponding plaintext, which unfortunately can make it difficult to read during decoding, as the alignment is critical. Alas, there were no hidden compartments or other special features.
The permutation is
Once again, the Caesar shift was specified with a number/plaintext pair.
1938 Radio Orphan Annie Pin


The 1938 pin was the largest of the Orphan Annie decoders, and arguably the most cryptographically sophisticated, owing to its independent mechanism for setting the Caesar shift. It was also a bit slow and error-prone to use, because it would only display a single ciphertext/plaintext pair at a time, with two different mechanisms to change either the number being decoded or the shift value.
The permutation is
The Caesar shift value was specified by a number from 1-26. A pointer on the back could be rotated to this number, which corresponded to a negative rotation of that many positions, calculated from 1=U. That is, at position 1, 1=Y; at position 2, 1=V; at 3, 1=L; at 4, 1=A; at 5, 1=E; at 6, 1=H, and so on up to 26, where 1=U. This allows the full range of 26 possible Caesar rotations, but does not directly reveal a plaintext/ciphertext pair. The disadvantage is that the the number reveals the relative shift value from one weekly message to another. So while this was a security gain for a single message, it can actually weaken the system as it was used over time.
Unfortunately, as we will see below, the key material (permutation) and design for this pin was somehow compromised and ended up in the hands of Captain Midnight, who re-used it in a very similar form for his Secret Squadron's badge a decade later. I think this constitutes a rather shocking security lapse, one that has never been fully explained by cryptologic historians. Personally, I suspect industrial espionage involving Horlicks.
1939 Radio Orphan Annie Pin


The 1939 pin slightly simplified the design, with a single window showing the current plaintext. It is far less discreet than previous editions; the words SECRET CODE appear prominently on the front, betraying its true purpose to anyone who looks. My sample is prone to slipping the shift setting when rotating the decoding digit, making it difficult to use under the high-stress field conditions that members of Annie's Secret Society likely encountered. The 1939 pins began the practice of assigning unique serial numbers, called the "OFFICIAL NUMBER", to each pin, permitting members of the secret society to use more rigorous accounting and control practices for their sensitive cryptologic items.
The permutation is
As with the 1938 pin, the 1939 pin had a separate setting on the back for the Caesar shift value. However, rotation markings are provided for only 8 different shifts (numbered 1-8) instead of all 26, skipping 2 or 3 positions between each.
1 2 3 4 5 6 7 8 1=I 1=H 1=X 1=R 1=L 1=P 1=B 1=A
While this mechanism had the advantage (as with 1938) of not revealing a plantext/ciphertext pair to specify the Caesar rotation, it weakened the system somewhat by supporting only fewer shifts.
1940 Radio Orphan Annie Pin



The 1940 edition was the last Radio Orphan Annie decoder pin. It is probably the most widely known to current generations, as it appeared as a prop in a famous scene in the 1983 film A Christmas Story. (The prop was authentic, but the coded message, which was truncated in several places, was fictional.) The decoder had an unusual design, resembling a gold coin (and with nothing identifying Radio Orphan Annie on the front). The code was stamped around the edge, with the Caesar shift set by rotating the front and back of the coin with respect to one another.
The permutation is
The 1940 decoder returned to the original (1937 and earlier) practice of specifying the Caesar shift with a plaintext/ciphertext pair. There was no independent mechanism for setting the shift.
Observant readers will notice that the 1940 permutation is very similar to that used in 1939, with a few letters swapped. Clearly, someone at the key generation division of Secret Society headquarters got lazy that year.
1941 Captain Midnight Badge


In 1941, Ovaltine switched its sponsorship from Orphan Annie to Captain Midnight, whose Secret Squadron, coincidentally, started issuing decoder badges to loyal Ovaltine drinkers. The 1941 badge has a design that looks (at first glance to my eye), remarkably similar (in size and shape) to an FBI special agent badge. I hope they serve Ovaltine at the FBI academy.
The permutation is
The Caesar shift could be set to one of 16 positions, through a somewhat confusing (and needlessly complicated) pair of windows on the back of the badge, labeled "Master Code" and "Super Code". The badge could be rotated until a digit from 1-8 appeared in one of the two windows. (The design was such that a number could appear in at most one of the two windows, so either a Master Code or a Super Code was used, not both). The listener was instructed to, e.g., "Set your badge to Master Code 5". These settings corresponded to the following ciphertext/plaintext mappings:
1 2 3 4 5 6 7 8 Master Code 1=N 1=G 1=F 1=H 1=B 1=D 1=C 1=U Super Code 1=L 1=S 1=J 1=P 1=X 1=E 1=K 1=Z
Note: In the 1990's, Klutz Press produced replicas of the 1941 badge. These badges look similar to the originals and have the correct permutation, but lack the Master Code and Super Code windows on the back. If you're tempted to buy a badge for a collection, make sure to check whether it's an original or a reproduction.
1942 Captain Midnight Photo Badge


The 1942 badge included a small slot for a photo, making it an early photo ID for Secret Squadron members. It was shipped with a default photo of Captain Midnight himself, as shown here.
The permutation is
The Caesar shift could be set to one of 6 "Master Codes" via a window on the back (no "Super Code" was used). These corresponded to the following ciphertext/plaintext mappings:
1 2 3 4 5 6 Master Code 1=Z 1=C 1=U 1=Q 1=V 1=A
Due to wartime shortages, new badges were not produced for 1943 or 1944. Secret Squadron messages in those years were encrypted with the 1942 badge.
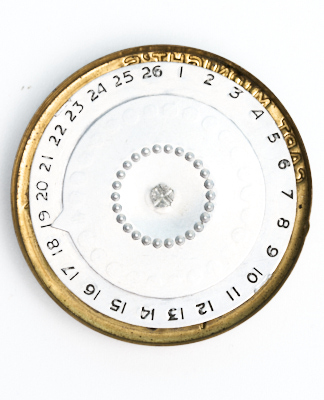
1945 Captain Midnight Badge


Captain Midnight finally produced a new badge in 1945. Probably due to continued shortages from the war, it was noticeably thinner than previous badges, and incorporated a plastic components for the first time. The center served as a moderate magnifying glass, presumably to assist squadron members in examining secret documents and clues.
The permutation is
The Caesar shift reverted to being specified by a single number/plaintext pair.
Astute readers will once again observe that the 1945 permutation is very similar to the 1942 badge, with a few letters swapped. This was especially unfortunate given that there was a war on. Axis cryptanalysts were no doubt laughing at this sloppiness.
1946 Captain Midnight Badge


The 1946 badge was similar in construction to the 1945 badge: thin stamped metal with a plastic rotor insert. The center knob had a mirrored surface.
The permutation is
As with the previous badge, the Caesar shift was given with a single number/plaintext pair.
1947 Captain Midnight Whistle


The 1947 decoder was a plastic whistle rather than a badge, with a rotating decoder on one side. The whistle was loud and shrill, no doubt to the delight of parents and neighbors of Secret Squadron members.
The permutation is
As before, the Caesar shift was given with a single number/plaintext pair.
1948 Captain Midnight Signal Mirror


The 1948 decoder was a key fob or dog tag rather than a badge. It had a signal mirror on the back, which could be removed to expose the shift settings. The mechanism is very similar to the 1938 Orphan Annie Pin.
The permutation is
The Caesar shift value was specified as a number from 1-26. The pointer on the internal mechanism could be rotated to this number, which corresponded to a negative rotation of that many positions, calculated from 1=U. That is, at position 1, 1=Y; at position 2, 1=V; at 3, 1=L; at 4, 1=A; at 5, 1=E; at 6, 1=H, and so on up to 26, where 1=U.
In a cryptologic blunder that is perhaps second only to the Venona decrypts (in which the Soviets disastrously re-used one-time pads), the key and offset scheme was not unique. It was copied directly from the Orphan Annie pin from 1938. How could this have happened? Was there some kind of secret cooperation between Annie and the Captain? Was the Ovaltine company compromised by spies? We may never know. Whatever happened, Secret Squadron message security was clearly put at risk by this mistake.
1949 Captain Midnight Decoder



The 1949 decoder, the last one issued, was also the most unusual design. It was not a badge, nor did it have any other obvious function except as a decoder. It employed internal gears (made of plastic) to display corresponding plaintext and ciphertext in two windows. A small (and presumably easily misplaced) key was used to disengage the gears to set different Caesar shifts.
The permutation is
The Caesar shift was specified by the usual single number/plaintext pair, using the supplied key to change the gearing. Hopefully squadron members hadn't lost their keys when it was time to decrypt a new message.